Did you know? BAI has partnered with CompTIA to become a pre-approved training provider. You can earn 1 CEU for each our of training. Our classes range from 1 day (8 CEUs) to 5 days (40 CEUs). At least 5o% of the training course content must relate to one or…
Read More
By Kathryn Daily, CISSP, CGRC (Formerly CAP), RDRP BAI’s training programs were developed with the information systems professional in mind. NIST’s Risk Management Framework is one of the most widely used governance, risk and compliance frameworks in the nation and forms the core of the ISC2 CGRC Exam Content (for…
Read More
By Amanda Lowell, Security+CE, RDRP Folks frequently reach out to BAI to ask, “Which security controls are required for X kind of DoD system?” It’s a valid question that can also be indicative of a common misconception. The short answer is, you will have certain control overlays for your information…
Read More
By Kathryn Daily, CISSP, CGRC, RDRP I know it’s a catchy headline, but it’s the wrong question to ask. NIST RMF and CSF are two totally different animals with a different purpose. NIST RMF is primarily focused on managing overall organizational risk, providing a structured approach…
Read More
By: Philip D. Schall, Ph.D., CISSP As many of you recall from an article written by Kathryn Daily in our January 2023 edition of RMF Today and Tomorrow titled CAP Becomes CGRC What Does this Mean? beginning February 15, 2023, ISC2 renamed the Certified Authorization Professional (CAP) certification to CGRC…
Read More

By Kathryn Daily, CISSP, CGRC, RDRP 🔒 Elevate Your Cybersecurity Career with RMF Training! 🚀🌐 In the ever-evolving landscape of cybersecurity, staying ahead is not just an advantage; it's a necessity. 🌐💡 That's why I'm passionate about highlighting the significance of Risk Management Framework (RMF) training for career growth in…
Read More
By, Amanda Lowell, Security+ CE, RDRP Special thanks to my colleagues Kathryn Daily and Sam Bodine for contributing to and helping edit this article!In the last few weeks, two different vulnerabilities found in Cisco’s software were disclosed to the public. Before you click away, thinking, “Well, I don’t own any…
Read More
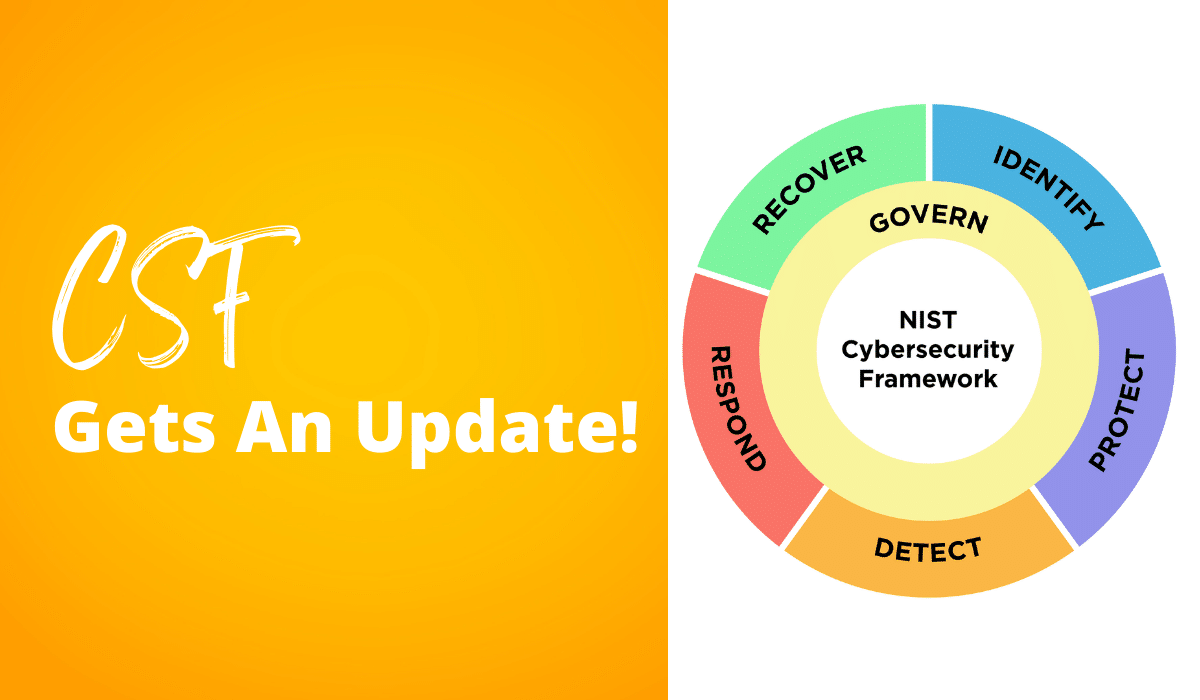
By, Kathryn Daily, CISSP, CGRC, RDRP Over a decade ago NIST published the Cybersecurity Framework as a base set of standards, guidelines, and best practices to manage cybersecurity risks for critical infrastructure. While it is currently voluntary for critical infrastructure, Executive Order 13800, May 11, 2017, required federal agencies to,…
Read More

by Lon J. Berman, CISSP, RDRP The year 2020 will be remembered for lots of things, not the least of which was the “great toilet tissue shortage.” Who can forget running from store to store, only to be confronted with empty shelves? 2020 was also the year the term “supply…
Read More
As of 4:30 eastern time, I was able to login to RMF Knowledge Service. Hopefully it's back for good.
Read More

